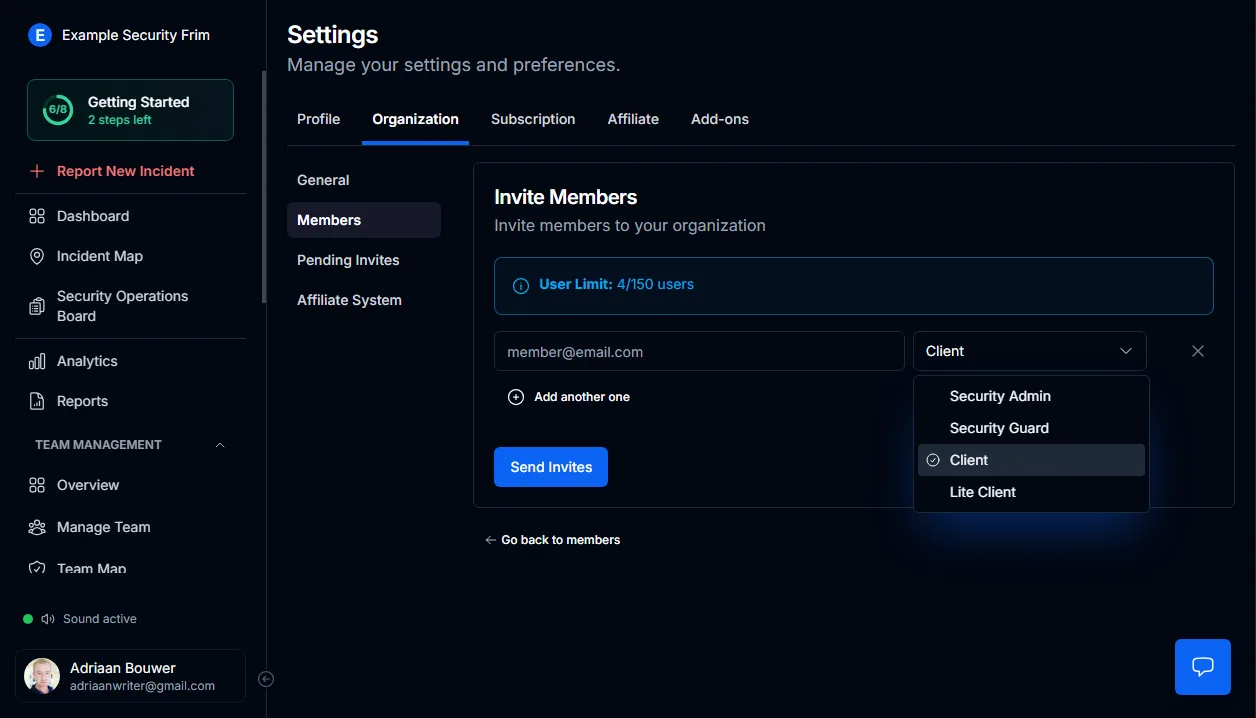
Four distinct roles, zero ambiguity
Every person in your control room dashboard operates under a defined permission tier. MyProtektor enforces four levels through the Team Management screen:
- Owners
- Admins
- Guards
- Private Clients
Each tier determines exactly what a user can view, edit, and act on. Boundaries are enforced by the system, not by trust.
Lock down sensitive operations
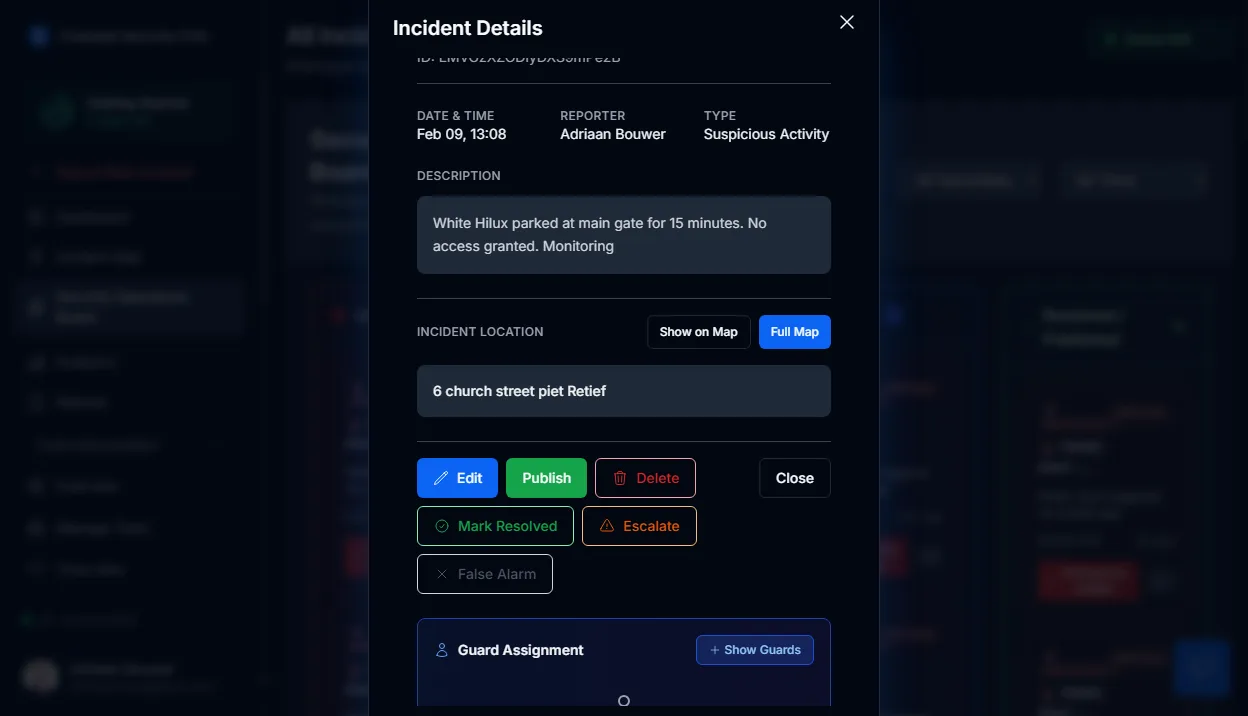
Internal threats and accidental changes are a real concern for security companies managing compliance-sensitive incident records.
- Guards submit reports but cannot modify or publish them
- Private Clients see only what has been approved for them
- Administrative functions remain gated behind Admin or Owner credentials
- System configuration is locked to authorised personnel
Sensitive data stays protected without relying on verbal agreements or manual oversight.
Visibility that keeps pace with growth
Scaling from ten guards to fifty introduces blind spots. MyProtektor eliminates them.
Through your dashboard you can:
- Review every active user and their assigned tier
- Identify roles at a glance without opening individual profiles
- Monitor last login and activity timestamps
- Revoke or downgrade access immediately
Departed staff and expired accounts never linger undetected.
Simpler workflows, fewer human errors
Restricting each user to their relevant tools creates a focused environment:
- New guards onboard faster because the interface shows only what they need
- Data entry mistakes decline when editing rights are limited
- Accountability becomes automatic since every action maps to one person
Structure is enforced at the platform level, removing the burden from supervisors.
Traceable records when it matters most
Permission tiers integrate directly with shift and duty management, connecting every recorded action to the person who was on duty at that moment.
When a dispute arises, the system provides:
- The exact role assigned at the time of the event
- The user identity attached to every logged action
- Precise timestamps of their last interaction
This creates a defensible record that protects the business during internal investigations or client queries.
Replacing outdated access habits
Shared passwords and open dashboards expose security companies to liability and data leaks.
Instead of:
- One login passed between multiple guards
- Vague assumptions about who can do what
- Open access where everyone sees everything
You operate with:
- Enforced permission boundaries per user
- Defined responsibility at every level
- A platform that maintains discipline automatically
The right information reaches the right person. Everything else stays hidden.
Step-by-step setup guides
Detailed walkthroughs are available in the admin documentation:
- Guard Management Guide — organise your team by role and manage individual access levels
- Profile Settings Guide — understand how each permission tier controls profile visibility and editing
Get Started
MyProtektor works on any Android or iOS smartphone. No special hardware needed.
View pricing plans to find the right package for your team.





